Log4j Developer Response – Cisco Blogs

As builders, we’re all waking as much as discover a newly found zero-day vulnerability (CVE-2021-44228) within the Apache Log4j library. If exploited, the vulnerability permits attackers to achieve full management of affected servers and your software. Like many builders, you’re in all probability scrambling to determine what methods are affected and the way to repair or patch this vulnerability.
And to make your job much more tough, Log4j is so extensively used that you could be not even understand the place in your methods it’s getting used. Many suppose that this Log4j vulnerability solely impacts your Java code. Sadly, this isn’t true. Log4j is a key element of many business and open-source options together with Apache Solr, Apache Struts2, Apache Fink, Apache Druid, Apache Kafka, Elasticsearch, and lots of extra.
Your problem now could be to comprise the specter of exploitation as rapidly as potential. There are a number of key issues you are able to do as a developer.
First, categorize your actions into three essential environments:
- Growth
- Check
- Manufacturing
Growth is simple. Simply be sure to find all utilization of Log4j 2.0-beta9 to 2.14.1 and improve to 2.15.0, which has the repair for this vulnerability. Replace the library in your undertaking and recompile. If updating the library requires any refactoring of your software that may take too lengthy, you should purchase a while by altering the runtime setting to stop exploits from working.
- In releases >=2.10, the susceptible conduct may be mitigated by setting both the system property log4j2.formatMsgNoLookups or the setting variable LOG4J_FORMAT_MSG_NO_LOOKUPS to true.
- For releases from 2.0-beta9 to 2.10.0, the mitigation is to take away the JndiLookup class from the classpath: zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class.
Your take a look at setting is sort of as easy. Simply add the additional step of pushing the up to date code to a take a look at setting the place your traditional automated and guide testing may be executed.
Manufacturing is the place it will get a bit trickier. As I’m certain you’re already involved about, these code adjustments might have an effect on your methods and enterprise. Some points to contemplate:
- How will any downtime have an effect on your prospects and what you are promoting? What workarounds are you able to rapidly supply to mitigate this downtime?
- What’s the impact of the repair? Do different methods combine with this technique? Does the affected system have an API that different methods name? Will the patch doubtlessly trigger cascading defects? You want sufficient time to completely take a look at.
- What different methods in your group might need this vulnerability? How are you going to observe these down and take a look at them?
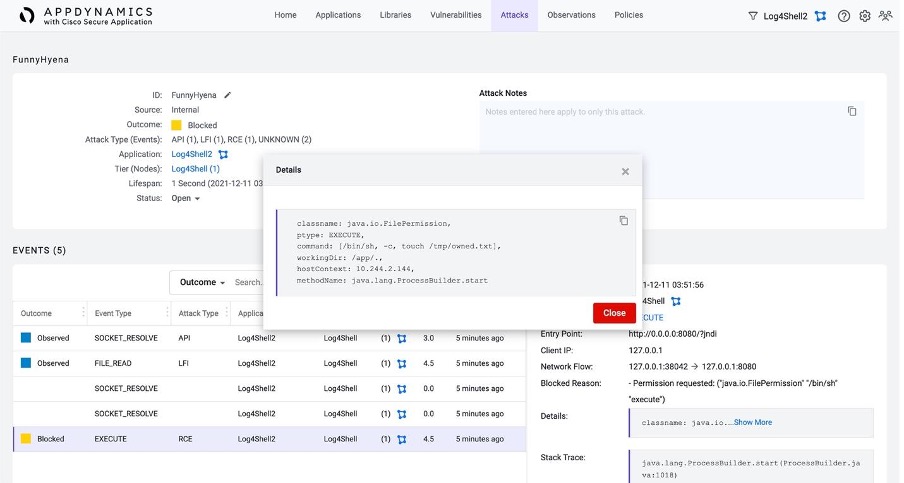
Discovering, fixing, and testing all of the affected methods might take days. Within the meantime, it’s good to defend your self now. Fortunately there are some readily-available options that may assist. These options assist discover the place the OSS vulnerability exists in your manufacturing setting in addition to mitigate the chance of the exploitation till the susceptible library may be upgraded. Choices for quick mitigation differ relying in your setting. One such resolution is AppDynamics with Cisco Safe Software, which is built-in into AppDynamics Java APM brokers.
Cisco Safe Software protects your manufacturing setting by:
- Figuring out what libraries your code is definitely utilizing in runtime
- Detecting the vulnerabilities in these libraries
- Detecting assaults whereas monitoring runtime conduct
- Defending methods with coverage to dam runtime exploit conduct
The primary, most essential motion to take is to search out out the place this vulnerability is introducing threat into your manufacturing setting. Cisco Safe Software tracks all library utilization and the accompanying vulnerabilities.

This distant code execution vulnerability permits the attacker to run any code in your software, which might lead to any variety of malicious runtime behaviors. One of many scariest of these is shell command execution that would enable for full management of not solely your software, however the underlying workload.
Cisco Safe Software will detect this shell command execution out of the field. It will also be configured to cease the command from executing in addition to ship occasions to your safety workforce for additional investigation.
Nevertheless, this received’t take away all the chance, so guarantee you’ve got plans to repair this vulnerability as quickly as potential. Evaluate the small print at Log4j’s safety disclosure.
Discover extra info on how AppDynamics with Cisco Safe Software gives full-stack software safety that may assist defend you from this and different vulnerabilities.
References
Share: