Who’s the Community Entry Dealer ‘Wazawaka?’ – Krebs on Safety

In an important many ransomware assaults, the criminals who pillage the sufferer’s community are usually not the identical crooks who gained the preliminary entry to the sufferer group. Extra generally, the contaminated PC or stolen VPN credentials the gang used to interrupt in have been bought from a cybercriminal intermediary generally known as an preliminary entry dealer. This submit examines among the clues left behind by “Wazawaka,” the hacker deal with chosen by a significant entry dealer within the Russian-speaking cybercrime scene.

Wazawaka has been a extremely energetic member of a number of cybercrime boards over the previous decade, however his favourite is the Russian-language neighborhood Exploit. Wazawaka spent his early days on Exploit and different boards promoting distributed denial-of-service (DDoS) assaults that would knock web sites offline for about USD $80 a day. However in newer years, Wazawaka has centered on peddling entry to organizations and to databases stolen from hacked firms.
“Come, rob, and get dough!,” reads a thread began by Wazawaka on Exploit in March 2020, during which he offered entry to a Chinese language firm with greater than $10 billion in annual revenues. “Present them who’s boss.”
In line with their posts on Exploit, Wazawaka has labored with not less than two totally different ransomware affiliate applications, together with LockBit. Wazawaka mentioned LockBit had paid him roughly $500,000 in commissions for the six months main as much as September 2020.
Wazawaka additionally mentioned he’d teamed up with DarkSide, the ransomware affiliate group chargeable for the six-day outage at Colonial Pipeline final yr that triggered nationwide gas shortages and value spikes. The U.S. Division of State has since provided a $5 million reward for info resulting in the arrest and conviction of any DarkSide associates.
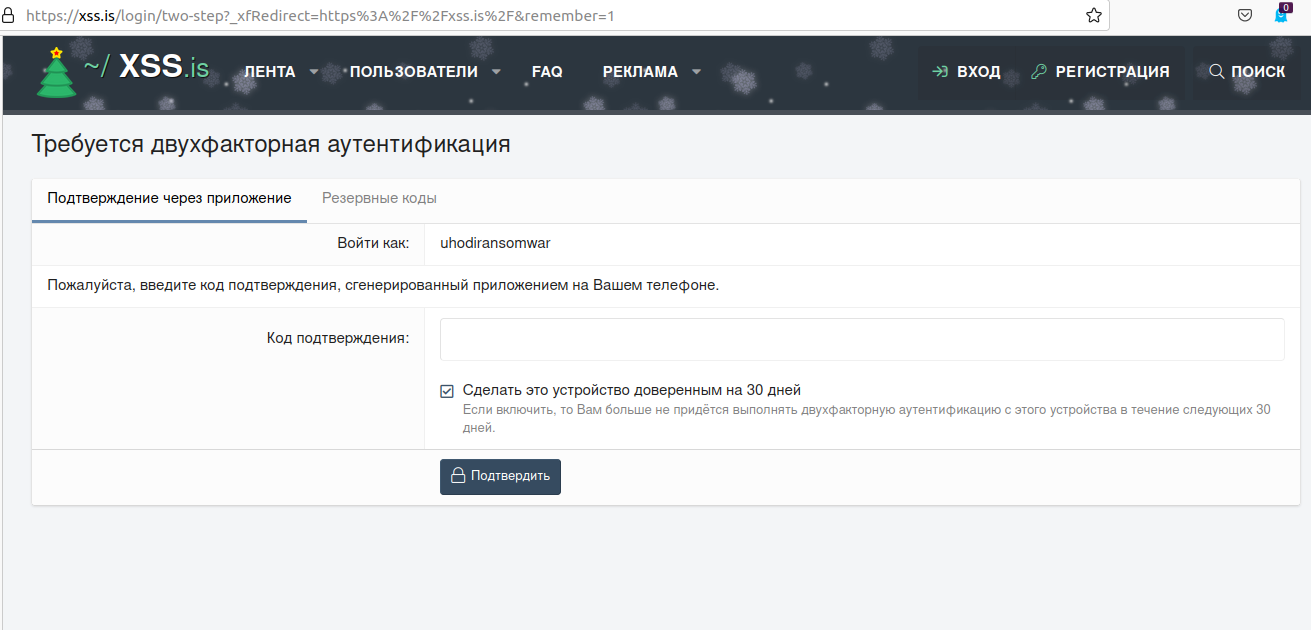
Wazawaka appears to have adopted the uniquely communitarian view that when organizations being held for ransom decline to cooperate or pay up, any knowledge stolen from the sufferer needs to be revealed on the Russian cybercrime boards for all to plunder — not privately offered to the very best bidder. In thread after thread on the crime discussion board XSS, Wazawaka’s alias “Uhodiransomwar” could be seen posting obtain hyperlinks to databases from firms which have refused to barter after 5 days.
“The one and the principle precept of ransomware is: the knowledge that you just steal ought to by no means be offered,” Uhodiransomwar wrote in August 2020. “The neighborhood must obtain it completely freed from cost if the ransom isn’t paid by the facet that this info is stolen from.”
Wazawaka hasn’t at all times been so pleasant to different cybercrooks. Over the previous ten years, his contact info has been used to register quite a few phishing domains meant to siphon credentials from individuals making an attempt to transact on varied darkish net marketplaces. In 2018, Wazawaka registered a slew of domains spoofing the actual area for the Hydra darkish net market. In 2014, Wazawaka confided to a different crime discussion board member through non-public message that he made good cash stealing accounts from drug sellers on these marketplaces.
“I used to steal their QIWI accounts with as much as $500k in them,” Wazawaka recalled. “A supplier would by no means go to the cops and inform them he was promoting stuff on-line and somebody stole his cash.”
WHO IS WAZAWAKA?
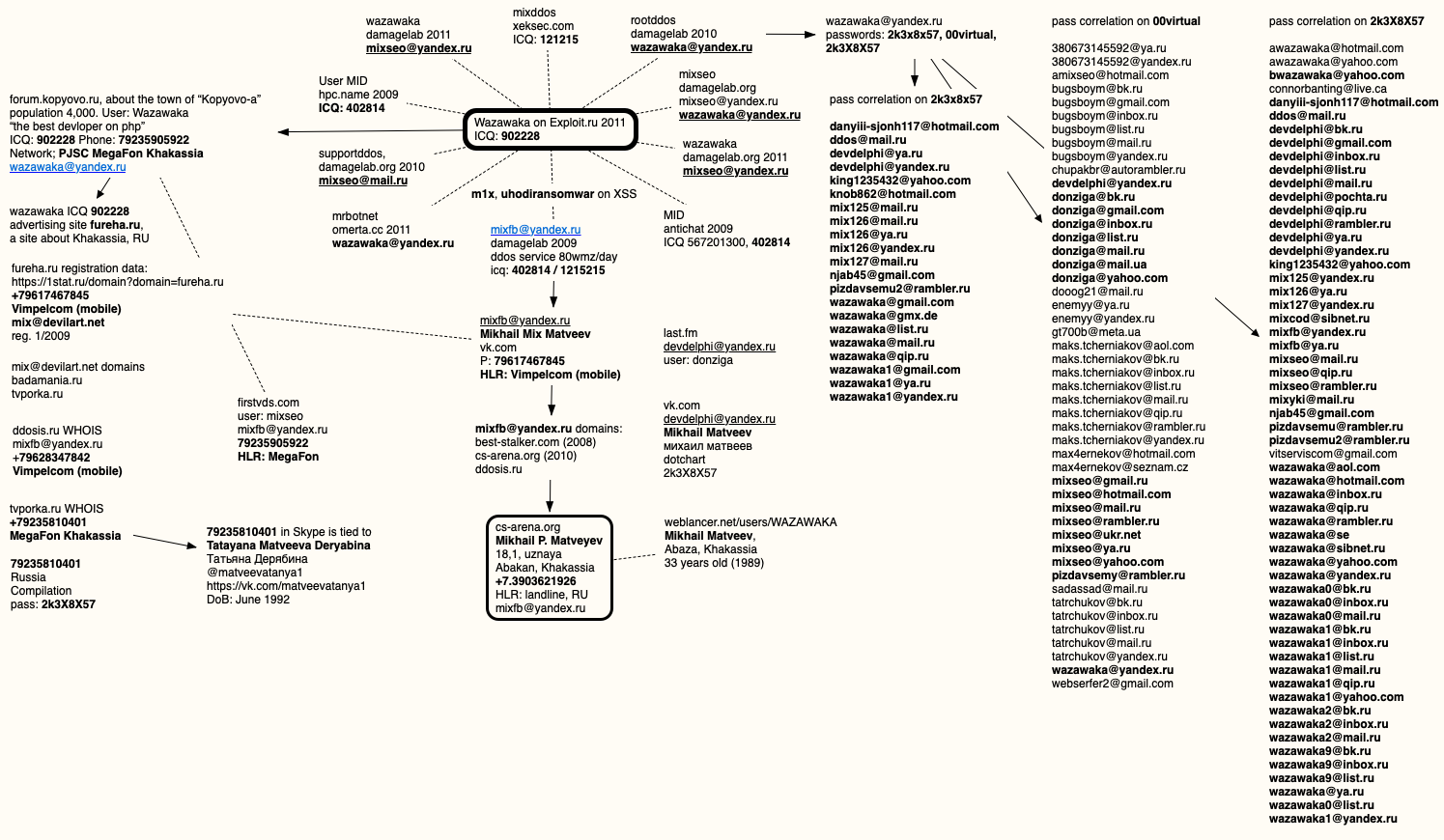
Wazawaka used a number of e-mail addresses and nicknames on a number of Russian crime boards, however knowledge collected by cybersecurity agency Constella Intelligence present that Wazawaka’s alter egos at all times used certainly one of three pretty distinctive passwords: 2k3x8x57, 2k3X8X57, and 00virtual.
These three passwords have been utilized by one or all of Wazawaka’s e-mail addresses on the crime boards through the years, together with [email protected], [email protected], [email protected], [email protected].
That final e-mail handle was used virtually a decade in the past to register a Vkontakte (Russian model of Fb) account beneath the title Mikhail “Combine” Matveev. The telephone quantity tied to that Vkontakte account — 7617467845 — was assigned by the Russian telephony supplier MegaFon to a resident in Khakassia, located within the southwestern a part of Japanese Siberia.
DomainTools.com [an advertiser on this site] experiences [email protected] was used to register three domains between 2008 and 2010: ddosis.ru, best-stalker.com, and cs-arena.org. That final area was initially registered in 2009 to a Mikhail P. Matveyev, in Abakan, Khakassia.
Mikhail Matveev is just not essentially the most uncommon title in Russia, however different clues assist slim issues down fairly a bit. For instance, early in his postings to Exploit, Wazawaka could be seen telling members that he could be contacted through the ICQ immediate message account 902228.
An Web seek for Wazawaka’s ICQ quantity brings up a 2009 account for a Wazawaka on a now defunct dialogue discussion board about Kopyovo-a, a city of roughly 4,400 souls within the Russian republic of Khakassia:
MIKHAIL’S MIX
Additionally round 2009, somebody utilizing the nickname Wazawaka and the 902228 ICQ handle began posting to Russian social media networks making an attempt to persuade locals to frequent the web site “fureha.ru,” which was billed as one other web site catering to residents of Khakassia.
In line with the Russian area watcher 1stat.ru, fureha.ru was registered in January 2009 to the e-mail handle [email protected] and the telephone quantity +79617467845, which is similar quantity tied to the Mikhail “Combine” Matveev Vkontakte account.
DomainTools.com says the [email protected] handle was used to register two domains: one referred to as badamania[.]ru, and a defunct porn website referred to as tvporka[.]ru. The telephone quantity tied to that porn website registration again in 2010 was 79235810401, additionally issued by MegaFon in Khakassia.
A search in Skype for that quantity reveals that it was related greater than a decade in the past with the username “matveevatanya1.” It was registered to a now 29-year-old Tatayana Matveeva Deryabina, whose Vkontakte profile says she at the moment resides in Krasnoyarsk, the most important metropolis that’s closest to Abakan and Abaza.
It appears probably that Tatayana is a relative of Mikhail Matveev, even perhaps his sister. Neither responded to requests for remark. In 2009, a Mikhail Matveev from Abaza, Khakassia registered the username Wazawaka on weblancer.web, a contract job alternate for Russian IT professionals. The Weblancer account says Wazawaka is at the moment 33 years outdated.
In March 2019, Wazawaka defined a prolonged absence on Exploit by saying he’d fathered a baby. “I’ll reply everybody in every week or two,” the crime actor wrote. “Grew to become a dad — went on trip for a few weeks.”
One of many many e-mail addresses Wazawaka used was [email protected], which is tied to a newer however since-deleted Vkontakte account for a Mikhail Matveev and used the password 2k3X8X57. As per common, I put collectively a thoughts map exhibiting the connections referenced on this story:
Analysts with cyber intelligence agency Flashpoint say Wazawaka’s postings on varied Russian crime boards present he’s proficient in lots of specializations, together with botnet operations, keylogger malware, spam botnets, credential harvesting, Google Analytics manipulation, promoting databases for spam operations, and launching DDoS assaults.
Flashpoint says it’s probably Wazawaka/Combine/M1x has shared cybercriminal identities and accounts with a number of different discussion board members, most of whom seem to have been companions in his DDoS-for-hire enterprise a decade in the past. For instance, Flashpoint factors to an Antichat discussion board thread from 2009 the place members mentioned M1x labored on his DDoS service with a hacker by the nickname “Vedd,” who was apparently additionally a resident of Abakan.
STAY TRUE, & MOTHER RUSSIA WILL HELP YOU
All of that is educational, after all, supplied Mr. Wazawaka chooses to a) by no means go away Russia and b) keep away from cybercrime actions that focus on Russian residents. In a January 2021 thread on Exploit concerning the arrest of an affiliate for the NetWalker ransomware program and its subsequent demise, Wazawaka appears already resigned these limitations.
“Don’t shit the place you reside, journey native, and don’t go overseas,” Wazawaka mentioned of his personal private mantra.
Which could clarify why Wazawaka is so lackadaisical about hiding and defending his cybercriminal identities: Extremely, Wazawaka’s alter ego on the discussion board XSS — Uhodiransomware — nonetheless makes use of the identical password on the discussion board that he used for his Vkontakte account 10 years in the past. Fortunate for him, XSS additionally calls for a one-time code from his cellular authentication app.
Wazawaka mentioned NetWalker’s closure was the results of its administrator (a.ok.a. “Bugatti”) getting grasping, after which he proceeds to evangelise about the necessity to periodically re-brand one’s cybercriminal identification.
“I’ve had some enterprise with Bugatti,” Wazawaka mentioned. “The man acquired too wealthy and started recruiting Individuals as affiliate companions. What occurred now’s the end result. That’s okay, although. I want Bugatti to do some rebranding and begin from the start 🙂 As for the servers that have been seized, they need to’ve hosted their admin panels in Russia to keep away from getting their servers seized by INTERPOL, the FBI, or no matter.”
“Mom Russia will enable you to,” Wazawaka concluded. “Love your nation, and you’ll at all times get away with all the pieces.”
In case you preferred this submit, you may additionally take pleasure in Who Is the Community Entry Dealer “Babam”?





Hey I am so thrilled I found your site, I really found you by accident, while I was researching on Askjeeve for something else, Anyhow
I am here now and would just like to say thanks a lot for a incredible post and a all round
exciting blog (I also love the theme/design), I don’t have time to
browse it all at the minute but I have book-marked it and also included your RSS feeds, so
when I have time I will be back to read much
more, Please do keep up the superb b.